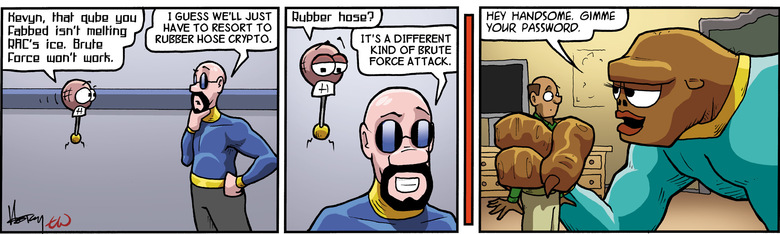
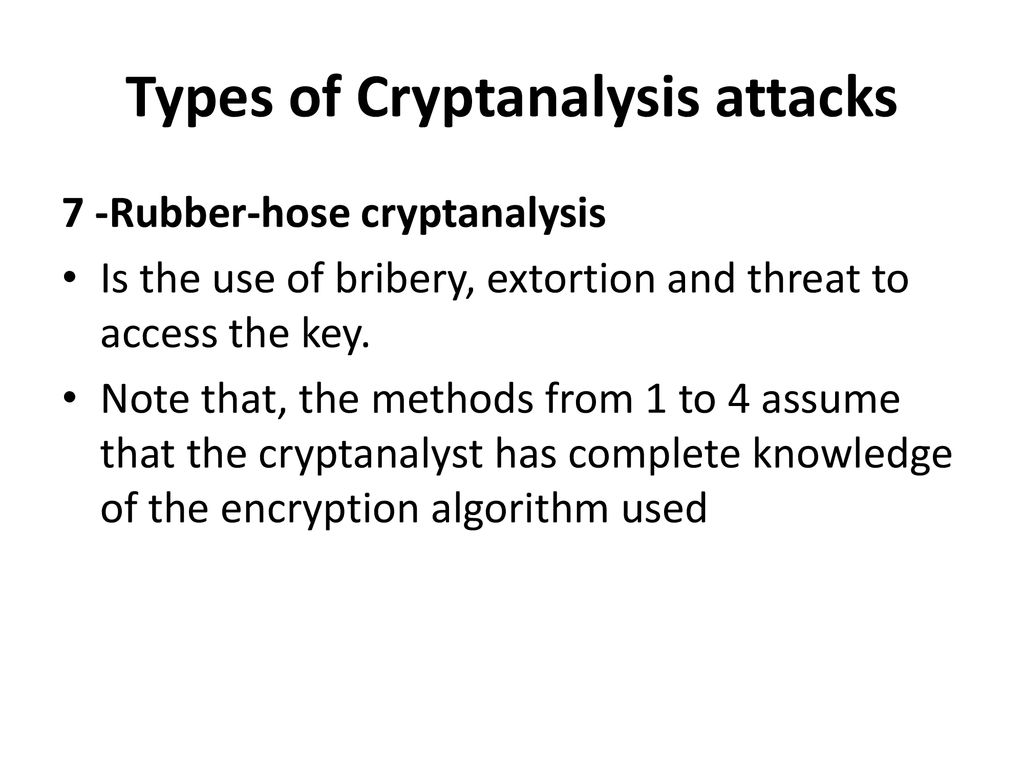
Anonymous Ghostwriters - Rubber Hose Cryptography works by filling the entire hard drive with random characters that are indistinguishable from encrypted data. The file system then takes each archive of real data
Shopping Girl Retro 30s Cartoon Rubber Hose Style" iPad Case & Skin for Sale by skullislandprod | Redbubble
Can't send PGP message that is encrypted, but not signed, since 5.200 · Issue #1961 · thundernest/k-9 · GitHub

What is a side channel attack? How these end-runs around encryption put everyone at risk | CSO Online