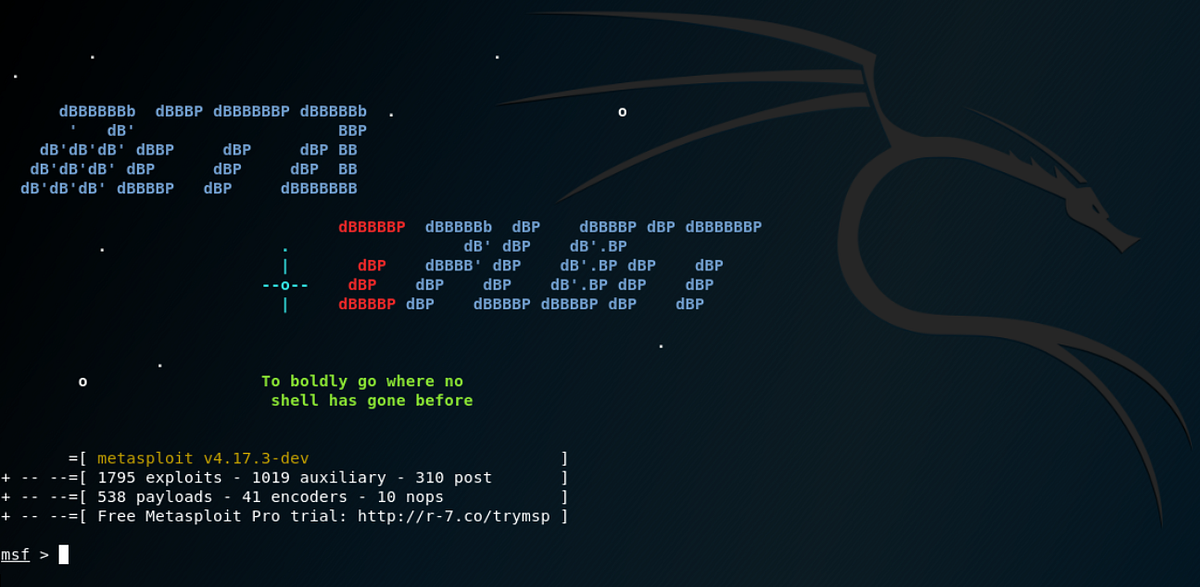
Kali Linux & Metasploit: Getting Started with Pen Testing | by Nicholas Handy | cyberdefenders | Medium

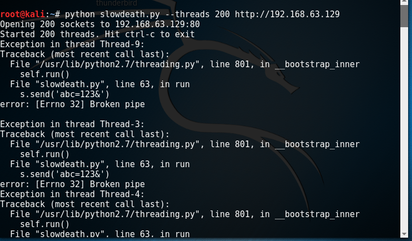
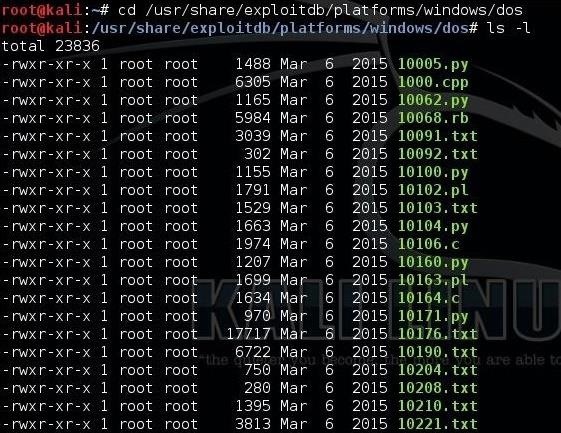
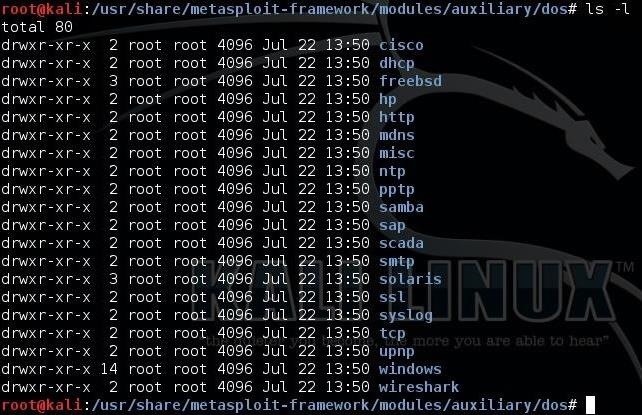
21D DoS Tools | DoS Attack using Metasploit | LOIC Tool for DoS Attack | DoS Countermeasures - YouTube

21D DoS Tools | DoS Attack using Metasploit | LOIC Tool for DoS Attack | DoS Countermeasures - YouTube




![Dos Attack On Window 7-[Metasploit] Dos Attack On Window 7-[Metasploit]](https://i.ytimg.com/vi/aZCL6yLr8yk/maxresdefault.jpg)