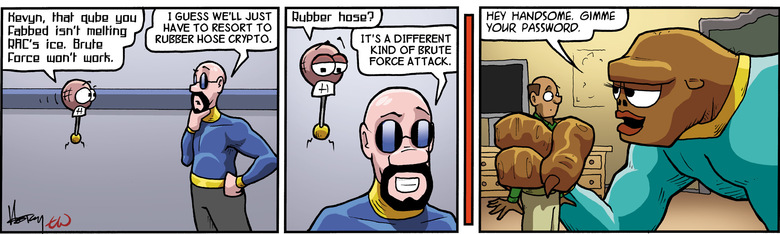
Amazon.co.jp: Rubber-Hose Cryptanalysis : Surhone, Lambert M., Timpledon, Miriam T., Marseken, Susan F.: Japanese Books
Reframing how you think about the concept of “managing your private keys” – Corey Petty's Personal Website

Amazon.it: Side-Channel Attack: Cryptography, Cryptosystem, Brute Force Attack, Electromagnetic Radiation, Key (Cryptography), History of Cryptography, Cryptanalysis, Rubber-Hose Cryptanalysis - Surhone, Lambert M., Timpledon, Miriam T., Marseken ...

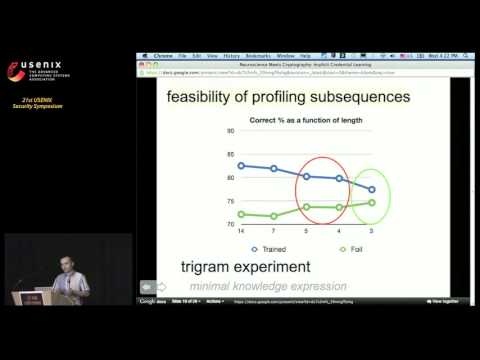
Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks | USENIX
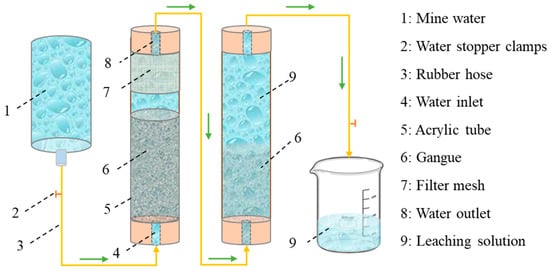
Water | Free Full-Text | Experimental Study on the Purification Mechanism of Mine Water by Coal Gangue

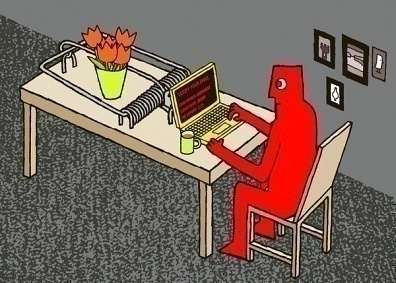
Programmer Humor on Twitter: "Cryptography: expectations vs. reality https://t.co/RD8Tfg057p https://t.co/IpB6X3VFtz" / Twitter

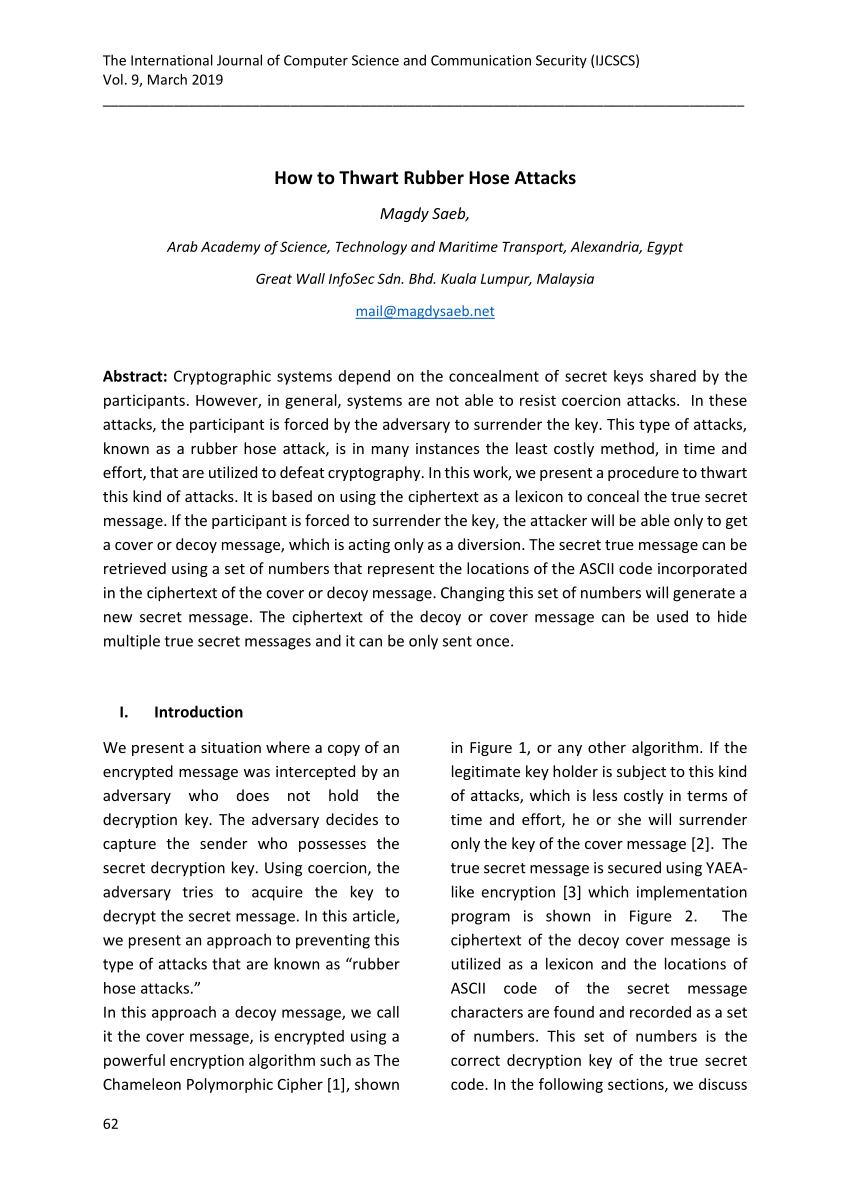
Anonymous Ghostwriters - Rubber Hose Cryptography works by filling the entire hard drive with random characters that are indistinguishable from encrypted data. The file system then takes each archive of real data

Neuroscience Meets Cryptography: Crypto Primitives Secure Against Rubber Hose Attacks | May 2014 | Communications of the ACM