Amazon.com: Pipe Fittings Accessories 1.5M Copper Core Shower Hose Adjustable Water Flow Steel Encryption Lightweight Handheld Hose Bathroom Shower Head Hose : Tools & Home Improvement
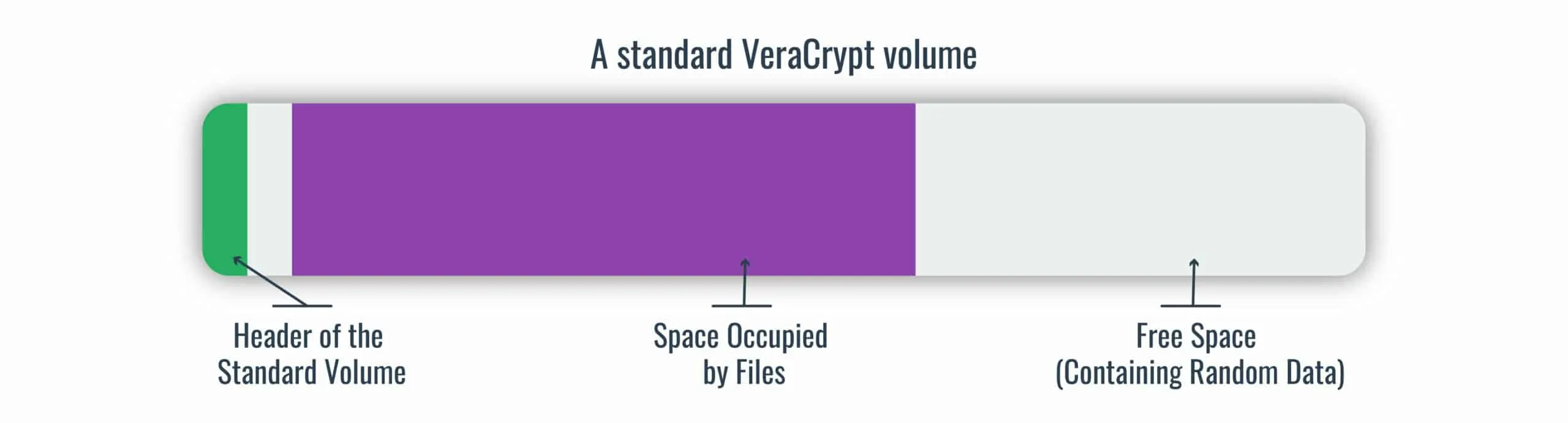
GitHub - Cookie04DE/Sekura: Encryption tool that's heavily inspired by the Rubberhose file system (https://en.wikipedia.org/wiki/Rubberhose _(file_system)).
Shopping Girl Retro 30s Cartoon Rubber Hose Style" iPad Case & Skin for Sale by skullislandprod | Redbubble

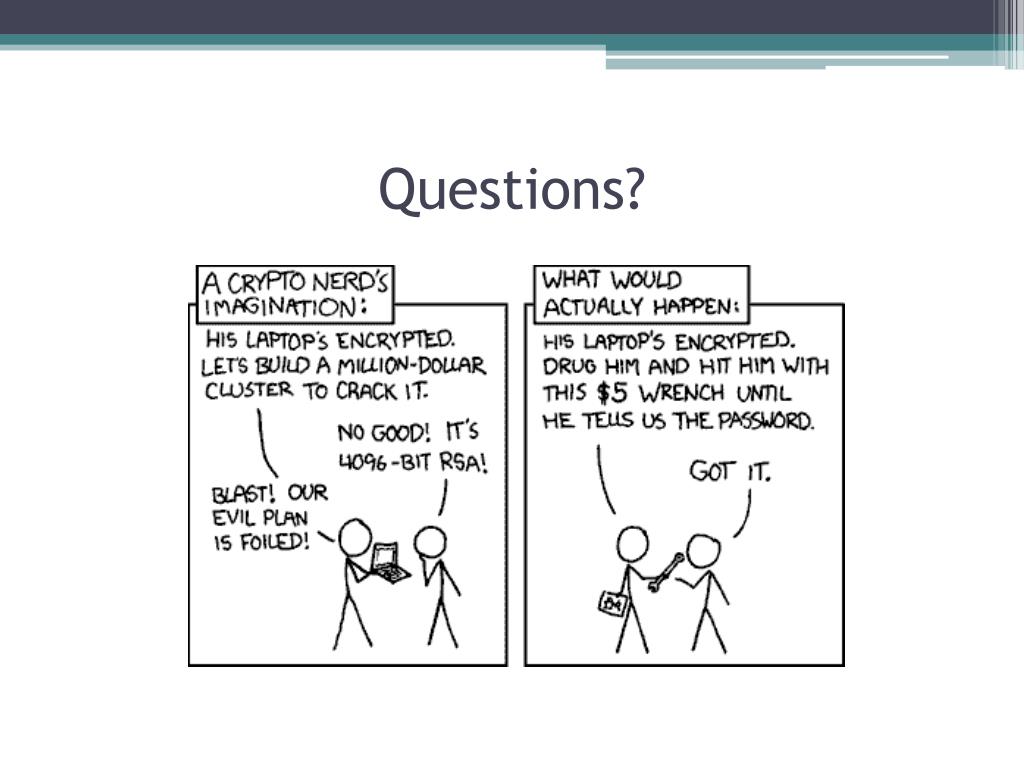
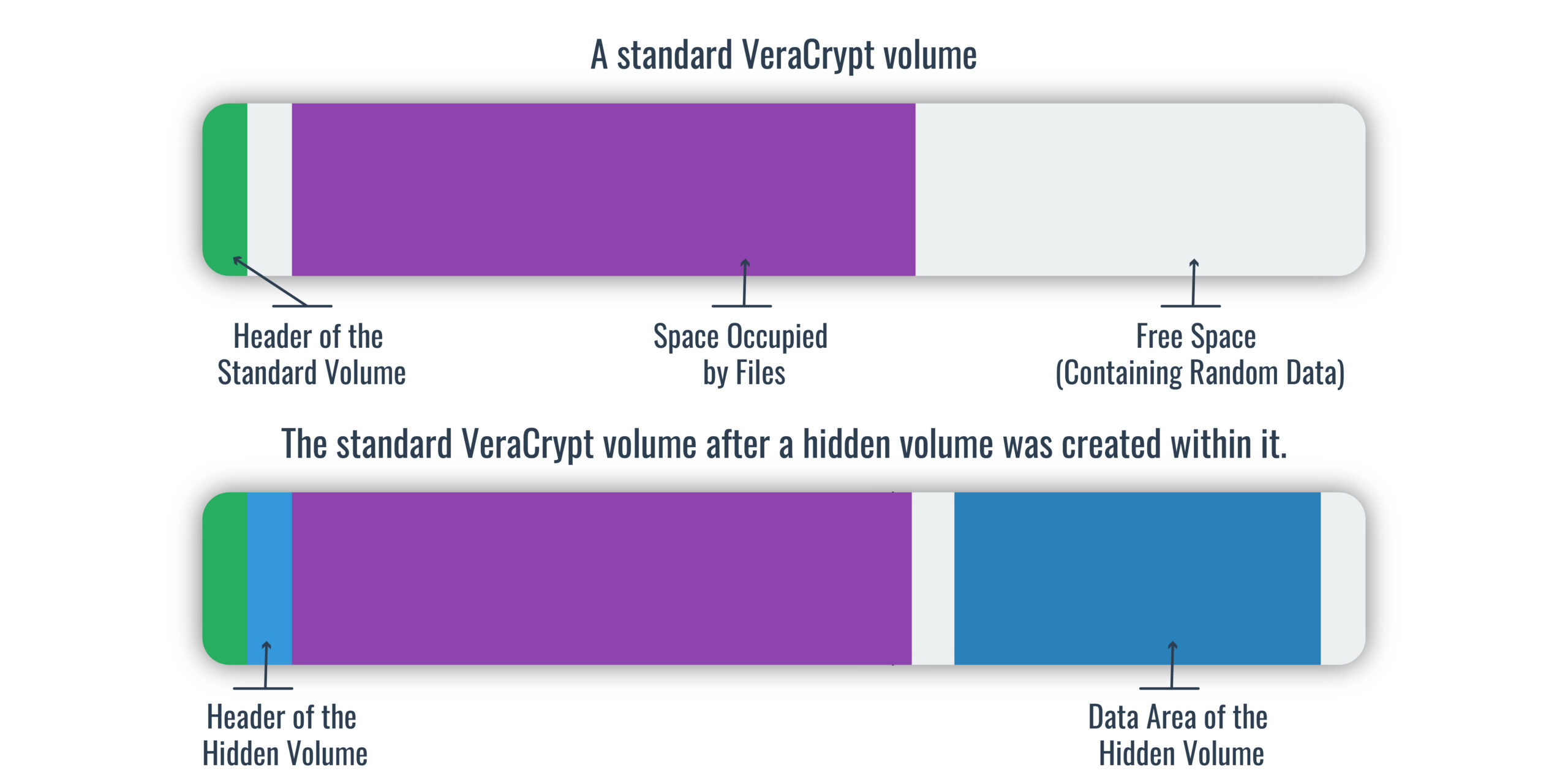
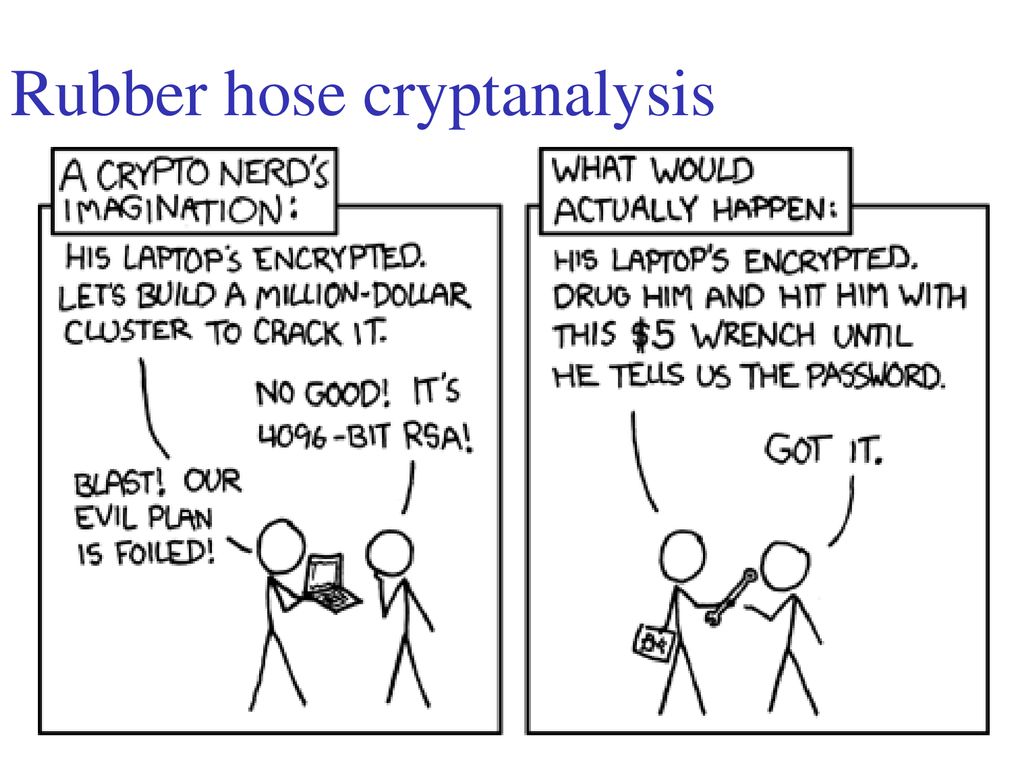
Anonymous Ghostwriters - Rubber Hose Cryptography works by filling the entire hard drive with random characters that are indistinguishable from encrypted data. The file system then takes each archive of real data